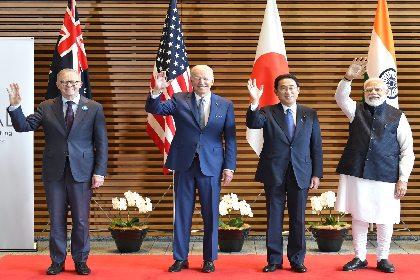
The narrative is the war
The Israel-Hamas War has shown the devastating impact of disinformation as a strategy of unconventional warfare. This narrative-led approach begins before hostilities start and seeks to set the agenda for leaders, their militaries and geopolitics. Democratic societies like India must prepare for similarly coordinated strategies and build societal resilience to manipulation.